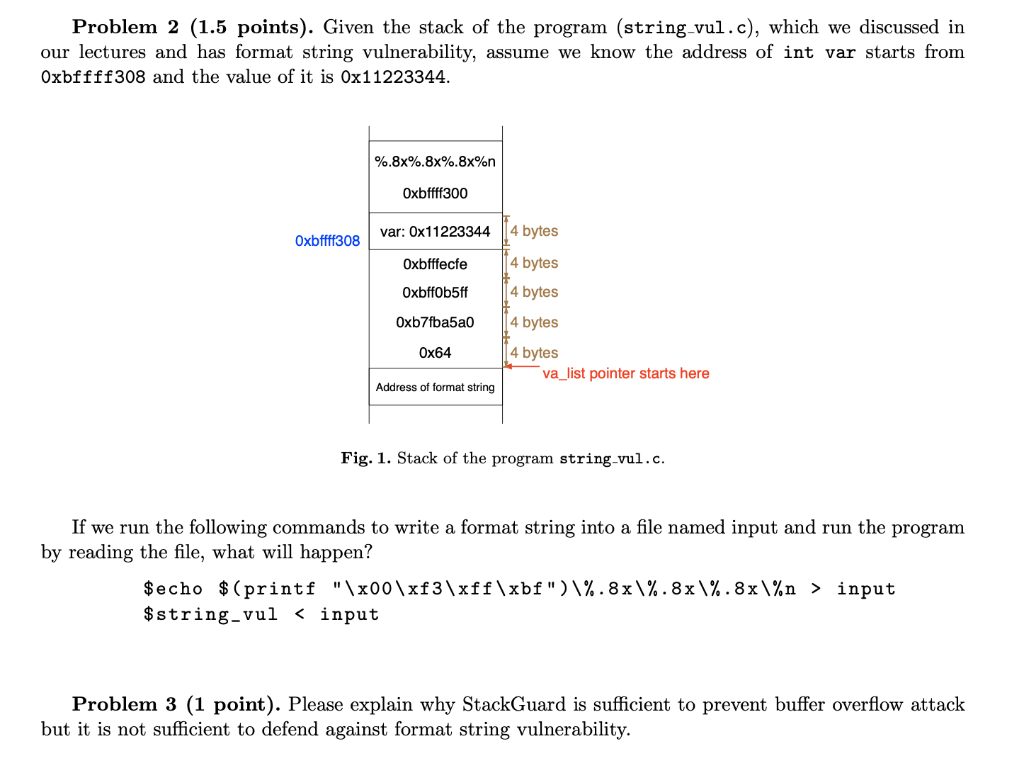
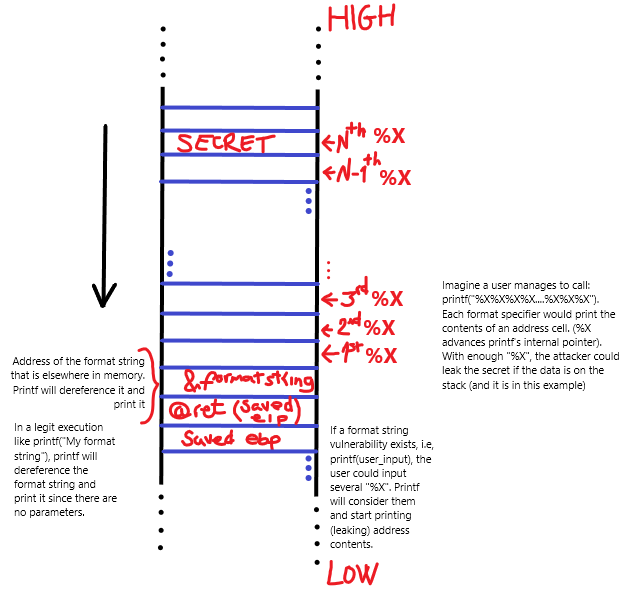
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother « Null Byte :: WonderHowTo
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother « Null Byte :: WonderHowTo


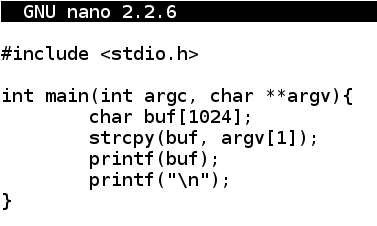


![PDF] Automated Format String Attack Prevention for Win32/X86 Binaries | Semantic Scholar PDF] Automated Format String Attack Prevention for Win32/X86 Binaries | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/88e085112063e3c80e2de0685c4359cfc3247d7d/5-Figure2-1.png)